SIMPLIFY YOUR PRIVACY COMPLIANCE
WE BUILD COMPLETE PRIVACY PROGRAMS THAT
PROTECT CUSTOMER DATA AND MEET REGULATIONS
Available Anywhere
Tailored privacy solutions, exceptional quality.
24/7 Support
Round-the-clock assistance, guidance.
Certified Advisors
Certified experts, profound insights.
Introducing the Privacy Dash Portal
Streamline Your Privacy Management with Privacy Dash
Say goodbye to the Privacy Playbook and hello to the Privacy Dash Portal – a comprehensive platform designed to centralize all your privacy management needs. Our innovative portal enables seamless planning, project execution, and access to our extensive range of privacy services. Privacy Dash ensures a user-friendly experience while maintaining the highest standards of data protection and compliance.
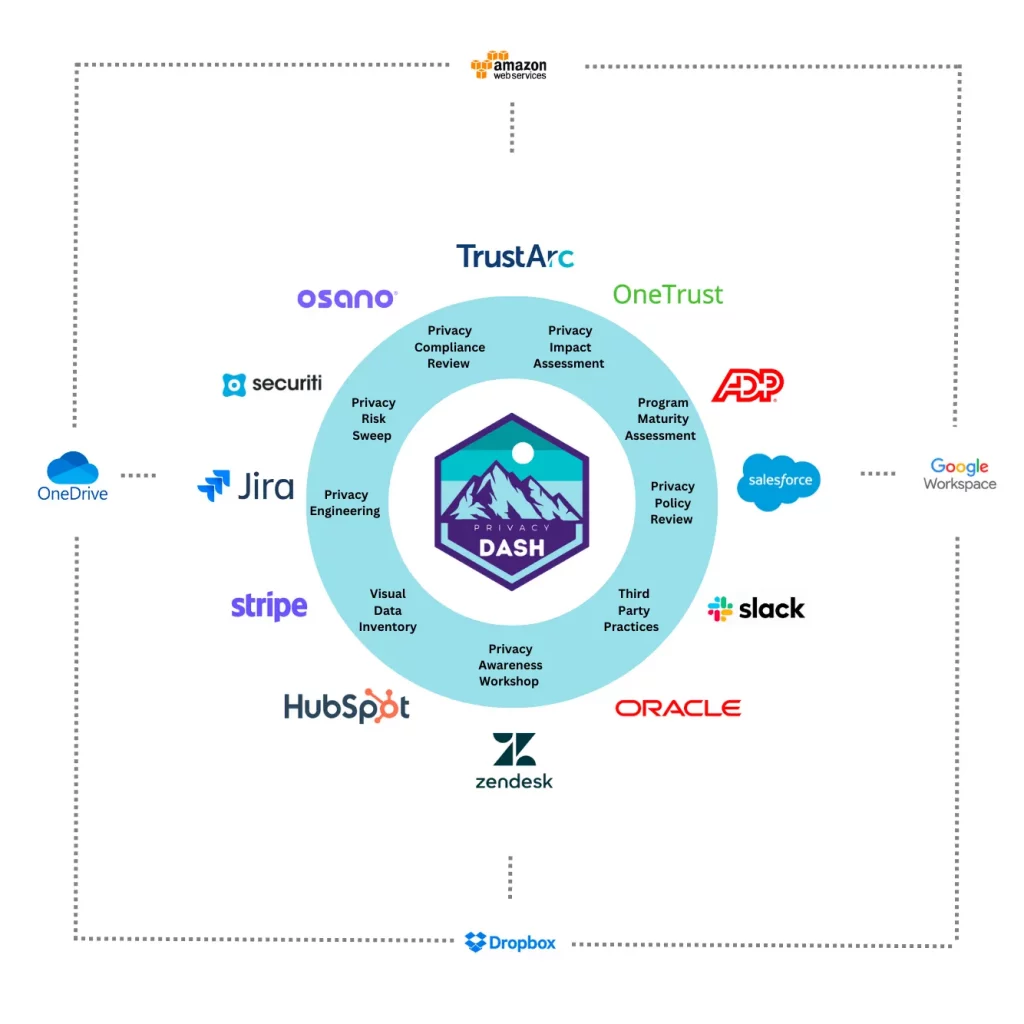
Our Privacy Services
Canada’s Largest Selection of Professional Privacy Solutions
Book your free 20-minute consultation to discuss a plan to better protect your customers and employees personal information
Privacy as a Competitive Advantage
Embrace the Power of Privacy Management
In today’s world, privacy is a precious commodity. By expertly managing privacy, your business can gain a competitive advantage, earning public respect and building trust with partners and customers. Managed Privacy Canada is here to guide you through this transformation, protecting privacy while improving your bottom line.
Managed Privacy Canada offers a wide array of professional privacy services tailored to your unique needs.
Enhance Your Privacy Management Experience
Introducing the Privacy Dash Mobile App
Elevate your privacy management experience by downloading the Privacy Dash Mobile App. Enjoy seamless access to privacy services, planning, and projects right at your fingertips.
To get started, simply visit the Privacy Dash on your smartphone and click “Install This App.” Take advantage of the convenience and flexibility of managing privacy on-the-go with our user-friendly mobile app.

















